- All Posts
- Banners
- Business
- BUSINESSES WE TAKE CARE OF IN BALTIMORE & WASHINGTON
- Case Studies
- Charles
- Clients
- Cyber Security
- Design
- Development
- Information Technology News & Information
- Reports
- Services
- Startup
- Tech Tips
- Technology
- Uncategorized
- Video Library

In the vast landscape of cybersecurity, the term “spoofing” holds a prominent place, representing a technique employed by malicious actors to deceive systems and users. This blog aims to shed light on the definition, meaning, and inner workings of spoofing, unraveling the complexities that surround this cybersecurity threat. Defining Spoofing: …

In an ever-evolving regulatory landscape, businesses must prioritize compliance to mitigate risks, build trust, and ensure long-term success. Strengthening compliance involves adopting a proactive approach, integrating compliance into the organizational culture, and staying abreast of regulatory changes. Explore key steps that businesses can take to fortify their compliance efforts and…

In our digital world, we have multiple devices and accounts to our name. This increases the risk of breaches and gives malicious actors access to sensitive information and account credentials. Biometric authentication revolutionizes how we verify ourselves when opening any secure account or device. This guide uncovers the benefits of…

As a modern business owner, you’re well aware of all the ways technology benefits your business while also putting it at risk. If you use Google Chrome as your browser of choice, you should be aware of the latest Google Chrome update malware scam. Keep reading to learn everything you…

Data breaches and security vulnerabilities are rising, and not everyone is safe from emerging threats. The NSA and CISA report that many businesses need to follow the best practices. Discover some of the most common business security mistakes and how to stay safe in this helpful guide. Default Login Credentials…

You can only make an online account with a username and password. The password manager tool in your web browser has an autocomplete function that quickly fills in your password field. This is handy but also makes you vulnerable to dangerous cyber activity. Learn why cybersecurity experts warn against using…

Modern technology makes it much easier to operate a business. However, it can also cause major issues if you somehow lose access to critical data within your network. That’s why having a backup solution is important so all your data remains safe and readily accessible. Discover the crucial role of data…

A new phishing campaign is making the rounds in an attempt for hackers to obtain sensitive information from vulnerable users. This campaign, first uncovered by tech researchers at Checkpoint, targets the popular cloud storage platform Dropbox. Learn more about the cybersecurity threat and how you can stay safe. Dangers of…
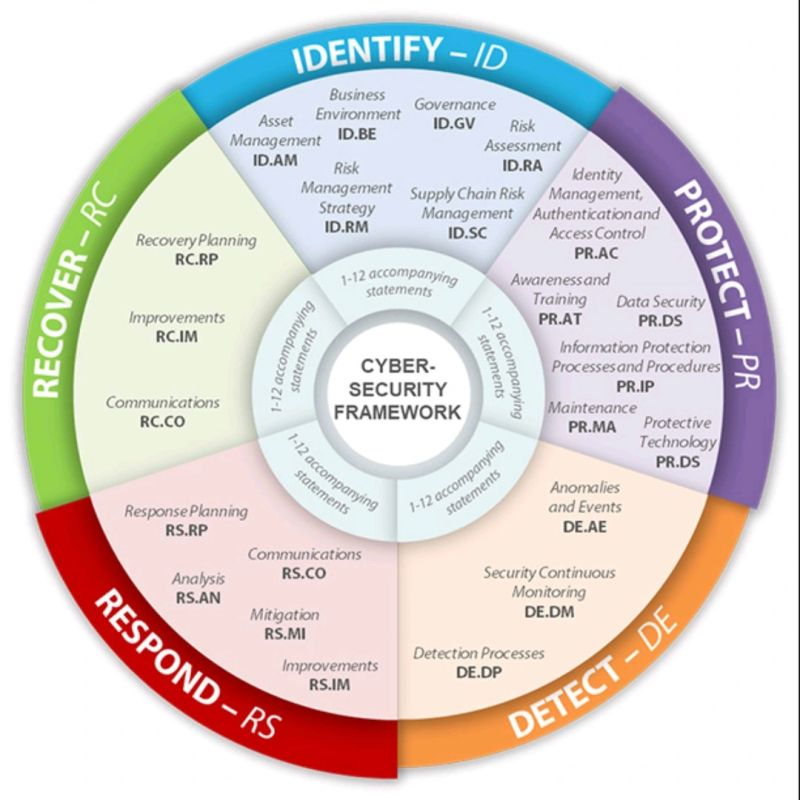
The NIST Cybersecurity Framework (CSF) stands as a cornerstone in the ongoing battle to secure our digital landscape. In today’s interconnected and data-centric world, safeguarding sensitive information and shielding organizations from cyber threats is paramount. At its core, the NIST CSF offers a comprehensive and adaptable approach to managing cybersecurity…

In the past, companies had to manage extensive computer networks on their own, purchasing servers and networking appliances and allocating physical space for data centers. However, the advent of cloud computing has transformed this landscape significantly. Today, companies can delegate most of their operations to the cloud, retaining only their…
